There are most likely as many myths about cybersecurity threats as there are respectable considerations. Some persons are nonetheless satisfied that smart speakers are recording their conversations 24/7, as an illustration, which might be impractical if it have been true. Accumulating audio from hundreds of thousands of customers would overwhelm datacenters, and supply principally ineffective noise, all for the prospect of determining whether or not to push an advert for engagement rings, e-bikes, or edamame.
The fact is definitely somewhat darker, in some methods. Hackers, companies, and governments needn’t wiretap your own home to study extra about you — usually there are subtler methods of going about it that do not immediately breach your privateness. Probably the most frequent instruments as of late is fingerprinting, which I am going to present a short clarification of, with some measures you may take to to dam it — should you really feel it is a significant issue, which it might not be relying in your circumstances.
What’s fingerprinting, and the way does it work?
A method round more durable boundaries
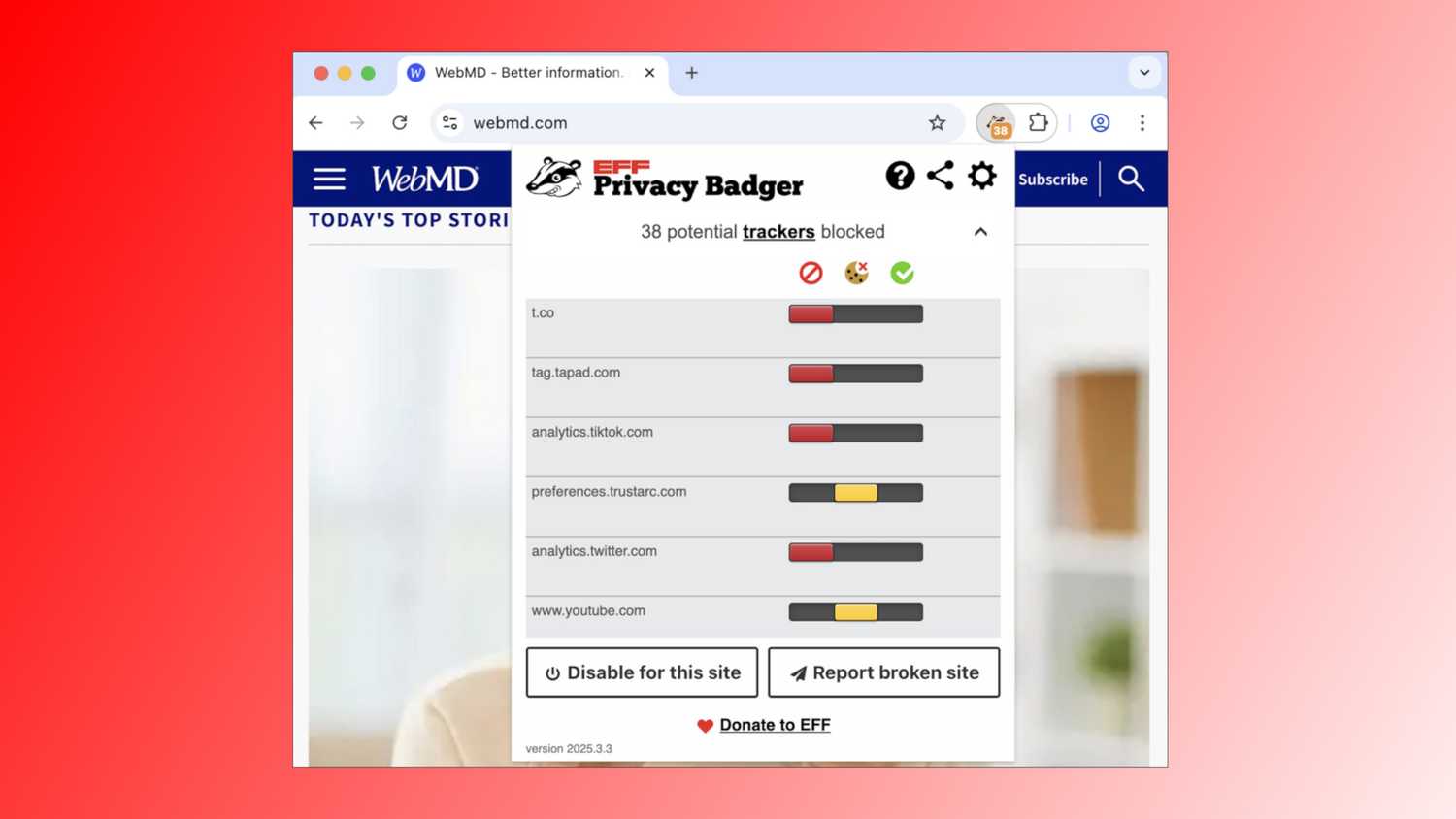
Through the years, web safety has tightened up in some ways. Any respected web site directs you to encrypted HTTPS when delicate knowledge is concerned, and you have little doubt encountered these cookie permission pop-ups, one thing required on account of laws. You may discover them annoying, however they’re a fast method of blocking undesirable monitoring. There are additionally browsers and plug-ins that may additional lock down cookies, such because the EFF’s Privacy Badger.
These kinds of issues can create a headache for advertisers and knowledge brokers, since their enterprise depends on focusing on particular demographics. There’s not a lot level aiming farm gear advertisements at a tech journalist, or PSAs for New York Metropolis trash pickup at somebody dwelling in Tokyo. In the meantime, hackers have fewer methods to intercept your knowledge than they as soon as did.
Fingerprinting is a workaround. There are two fundamental types: energetic and passive fingerprinting. The primary includes pinging your gadget with knowledge packets, then gauging the way it responds. The second includes monitoring community site visitors or browser knowledge, in essence, ready so that you can come to the tracker.
Fingerprinting maps a wide range of signatures that do not imply a lot on their very own, however collectively slim down your identification.
Both method, fingerprinting does not immediately accumulate your private information, which is commonly encrypted or anonymized anyway. As a substitute it depends on mapping a wide range of signatures that do not imply a lot on their very own, however collectively slim down your identification in a method that may be adopted if these signatures reappear elsewhere.
To illustrate you are visiting an internet site in your cellphone. To speak correctly, that web site must know your IP tackle, which can be utilized to get a tough sense of your geographical location. It additionally must know what gadget, browser, and working system you are utilizing to render the location correctly. When you mix that with different particulars like language, decision, and font settings, it turns into more and more clear {that a} particular individual is visiting, even when you do not know their title and residential tackle.
Energetic fingerprinting can doubtlessly accumulate much more knowledge, comparable to open community ports, however that is not essentially fascinating, as a result of it may be detected by safety software program. Hackers could use this kind of probing to determine weak factors for assault.
Why is fingerprinting a hazard?
Exploring the larger and lesser dangers
To be clear, there are genuinely useful makes use of of fingerprinting. It may be a method for websites to filter out bot site visitors, and it is one methodology organizations use to guard you towards financial institution fraud and different types of identification theft. In the event you usually store in Austin, however transactions out of the blue begin occurring in Hong Kong with out a flight in between, that is a crimson flag.
For most individuals, I think about, the final objection to fingerprinting is that it looks like a violation of privateness. Some folks resent the thought of being adopted and focused for advertisements regardless of taking different measures to safeguard their identification, comparable to blocking cookies. Your objections may be even stronger in direction of the thought of events like knowledge brokers promoting your knowledge with out specific consent.
Often, until you’ve gotten a particular purpose to be involved, the one folks eager about focusing on you’re advertisers and knowledge brokers.
As I discussed, fingerprinting can be used for extra insidious functions, comparable to studying all the pieces essential to launch a tool hack. Worse than that’s the prospect of surveillance. Criminals and governments alike could possibly comply with you across the web, gaining an much more detailed image of your life over time. If this knowledge might be correlated with real-world names and addresses, it may be used for functions like stalking and robberies within the case of criminals, or arrest and intimidation within the case of governments. Below an authoritarian regime, it is not out of the query that fingerprinting might get somebody tortured or killed.
Do not panic. Often, until you’ve gotten a particular purpose to be involved, the one folks eager about focusing on you’re advertisers and knowledge brokers. Random assaults aren’t unattainable, however you are already profitable as a client.
How can I defend myself towards fingerprinting?
Some easy and not-so-simple steps
The primary consideration is limiting your on-line presence. The less apps and web sites you utilize, the much less possible you’re to be fingerprinted, and the smaller your general historical past might be. Delete any apps and accounts you are now not utilizing. While you do register to one thing, take note of any probability to choose out of a service amassing or sharing your knowledge. That is hardly bulletproof safety towards fingerprinting, but it surely’s a step.
The subsequent step includes software program. Some browsers and plug-ins make anti-fingerprinting expertise a promoting level. Other than Privateness Badger, one other instance is Brave, a browser with variations for Android, iPhone, iPad, Home windows, Mac, and Linux. Probably the most excessive browsers is Tor, which I would truly suggest towards utilizing for informal functions, since its relay community slows down site visitors, and it scrubs all cookies and browser historical past everytime you’re completed — even entries that merely bear in mind your web site preferences.
Some browsers and plug-ins make anti-fingerprinting expertise a promoting level, a couple of examples being Courageous, Tor, and the EFF’s Privateness Badger add-on.
If Tor feels like an excessive amount of, you may contemplate making an attempt a extra standard VPN (digital personal community). Any VPN will robotically bounce your site visitors via a distant server, whether or not in a special metropolis or a special nation. You may nonetheless have to mix this with anti-fingerprinting software program, nevertheless, as a result of a VPN principally simply encrypts your site visitors and hides your IP tackle. Actually, if there is a discrepancy between your gadget clock and the server you are connecting from, that will truly make your presence simpler to identify.
You must also take the time to discover distinctive app, gadget, and browser settings that may additional restrict what’s shared. Disabling JavaScript will block some fingerprinting scripts, for instance, and eradicating pointless extensions will make your browser look extra generic.
That final tip factors to what you are making an attempt to realize general: mixing in with the gang. In a giant metropolis, there’s most likely hundreds of individuals utilizing Chrome or Safari on their gadget at any given time. In the event you follow well-known websites, solely use a privateness blocker extension, and join with a faux IP tackle, there’s solely a lot that may be gleaned about you.
Trending Merchandise

Logitech MK825 Performance Wireless...

Acer SH242Y Ebmihx 23.8″ FHD ...

Logitech MK345 Wireless Keyboard an...

GAMDIAS ATX Mid Tower Gaming Pc PC ...

Logitech Signature MK650 Combo for ...

NZXT H9 Move Twin-Chamber ATX Mid-T...

Acer KC242Y Hbi 23.8″ Full HD...

ASUS RT-AX5400 Dual Band WiFi 6 Ext...

Lenovo Ideapad Laptop Touchscreen 1...